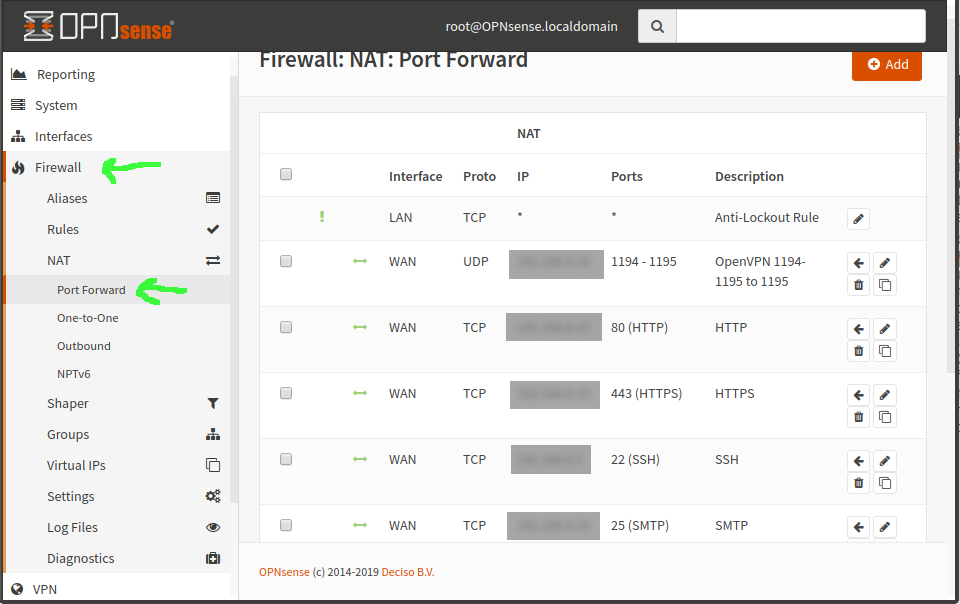
You’ve got a server on the LAN running OpenVPN, WireGuard, or some other VPN service. You port forwarded the VPN service port to that box, which was easy enough, under Firewall–>NAT–>Port Forward.
But now you need to set a static route through that LAN-located gateway machine, so that all the machines on the LAN can find it to respond to requests from the tunnel—eg, 10.8.0.0/24.
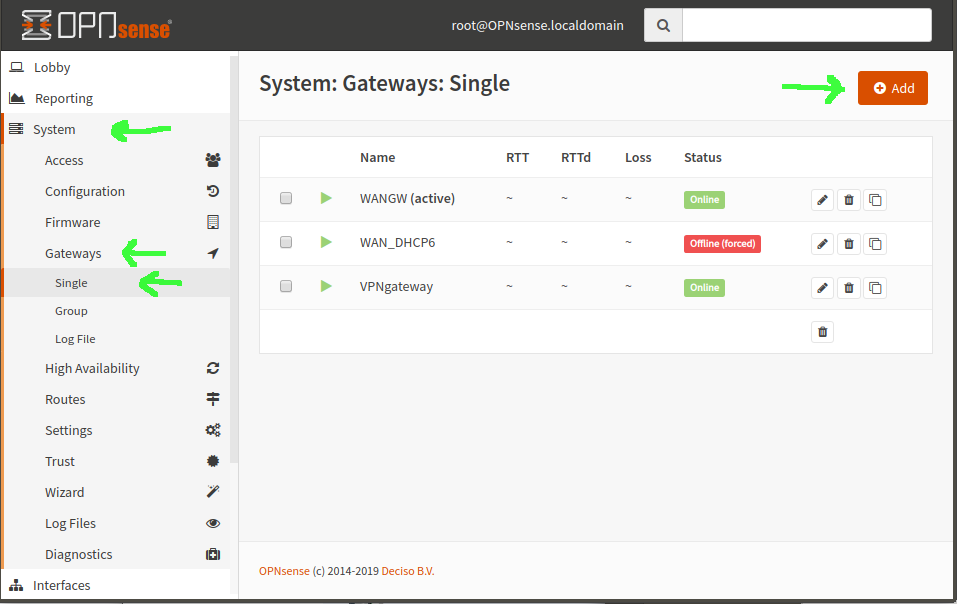
First step, in either OpnSense or pfSense, is to set up an additional gateway. In OpnSense, that’s System–>Gateways–>Single. Add a gateway with your VPN server’s LAN IP address, name it, done.
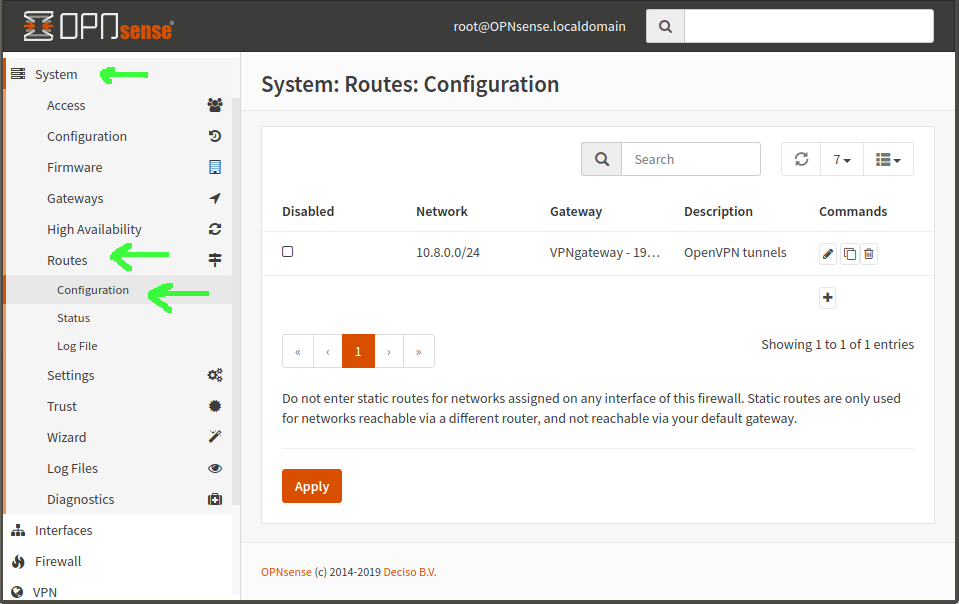
Now you create a static route, in System–>Routes–>Configuration. Network Address is the subnet of your tunnels—in our example, 10.8.0.0/24. Gateway is the new gateway you just created. Natch.
At this point, if you connect into the network over your VPN, your remote client will be able to successfully ping machines on the LAN… but not access any services. If you try nmap from the remote client, it shows all ports filtered. WTF?
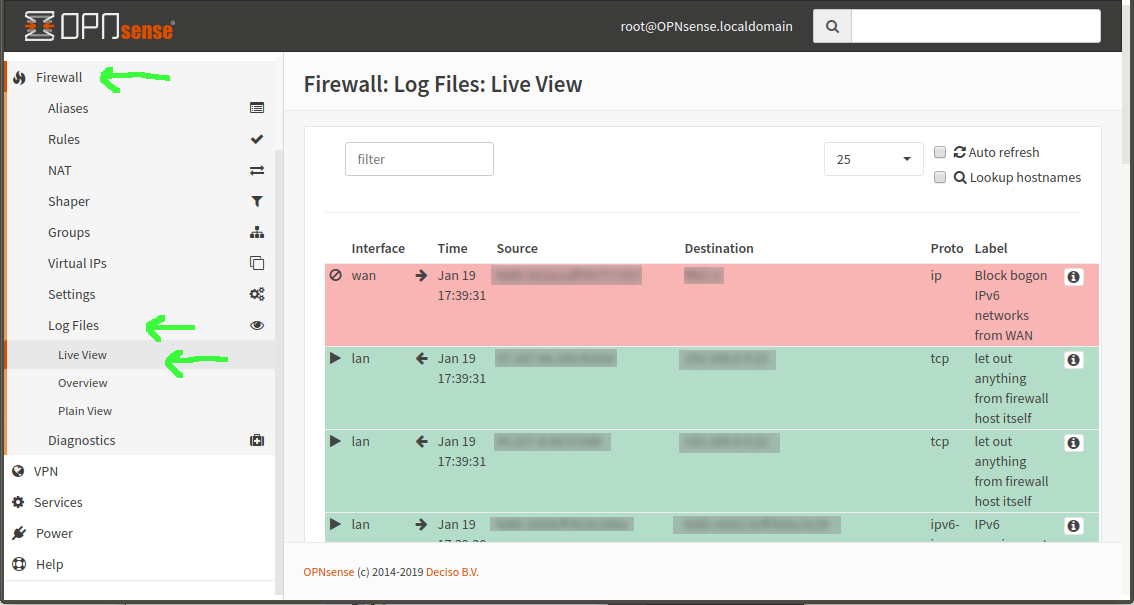
Diagnostically, you can go in the OpnSense GUI to Firewall–>Log Files–>Live View. If you try something nice and obnoxious like nmap that will constantly try to open connections, you’ll see tons of red as the connections from your remote machine are blocked, using Default Deny. But then you look at your LAN rules—and they’re default allow! WTF?
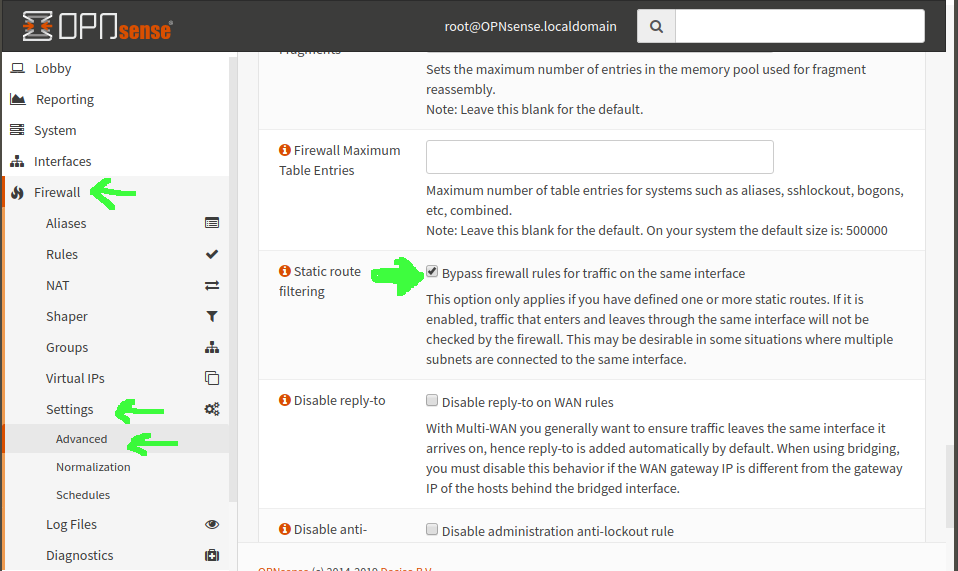
I can’t really answer W the F actually is, but I can, after much cursing, tell you how to fix it. Go in OpnSense to Firewall–>Settings–>Advanced and scroll most of the way down the page. Look for “Static route filtering” and check the box for “Bypass firewall rules for traffic on the same interface”—now click the Save button and, presto, when you go back to your live firewall view, you see tons of green on that nmap instead of tons of red—and, more importantly, your actual services can now connect from remote clients connected to the VPN.
Hey, I am interested in OPNsense, what is the difference with pfSense ? Is it better than Linux based solutions ? I would like to replace my proprietary home router with a custom solution.
I don’t know of any up-to-date Linux-based router distros that I’d trust. There’s certainly nothing wrong with Linux networking, just for whatever reason the Linux-based router distros, specifically, seem to have either aged out with insufficient maintenance or gone proprietary so far as I know.
It’s early days with opnsense for me, but so far I prefer it significantly to pfsense.
Super great guide – took me ages to find this! (you should defo repost links to these now and again on your Twitter feed!)
One thing I wanted to point out: in my testing port-forwarding is still, as of December 2020, not working in WireGuard on OPNsense (or at all, I think). Took me a long time to debug this, drove me crazy, late nights etc, but seems that it’s still super new in this regard. Hope that helps someone!